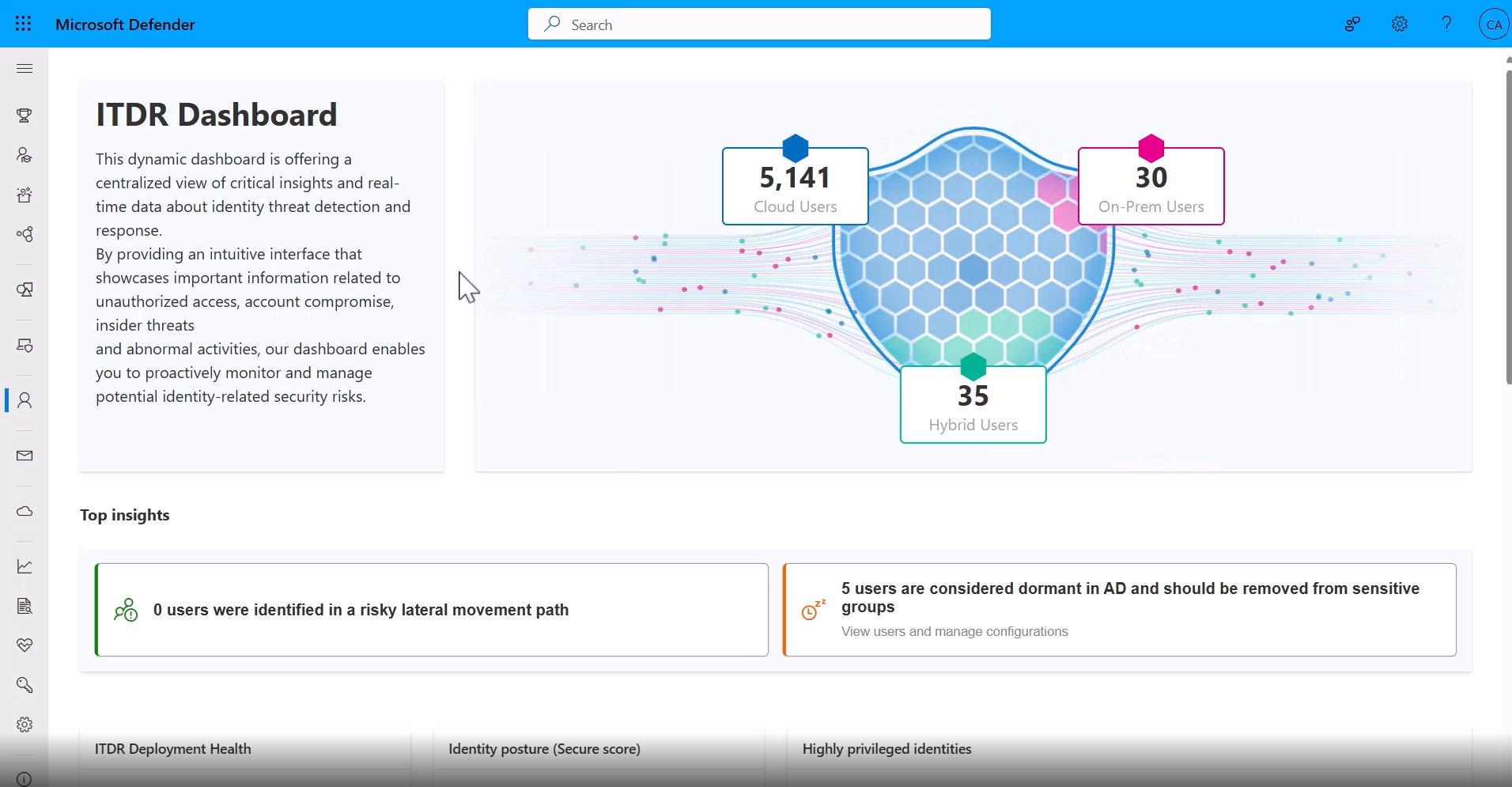
Overview
Identity threat detection and response for the SOC
Use Defender for Identity to deliver enriched identity insights and help your security operations teams better prevent, detect, and respond to identity-based cyberthreats.
Comprehensive protection
Gain a deeper understanding of your organization’s unique identity landscape. Dedicated sensors and connectors provide rich insights into the identities, environments and applications that make up your identity fabric. These signals are then automatically correlated with data from other security domains to further augment and enrich insights across the platform.

Security context
Surface identity-specific identities to streamline your security hardening, incident investigation, and threat-response initiatives.
Intelligent automation
Automate response to identity threats and compromised identities to stop identity cyberattacks in real time.

Capabilities
Key capabilities
Prevent, detect, and respond to advanced identity threats across your identity fabric with Defender.
| Capabilities | |
|---|---|
| Dedicated sensors for on-premises infrastructure | Specialized sensors monitor critical on-premises identity infrastructure to provide unparalleled visibility and protection. |
| Native integration with Microsoft Entra ID | Integration between Microsoft Entra and Defender for Identity fosters collaboration across identity and security teams with consistent data, alerts, and workflows across teams and experiences. |
| Purpose-built connectors | Platform-level connectors bring insights from cloud identity providers and other elements of modern identity fabrics to further extend protection and enrich your understanding of your overall identity footprint. |
| Proactive posture and vulnerability management | Minimize your cyberattack surface area and harden your security posture with identity-specific recommendations to resolve vulnerabilities and close potential attack paths. |
| Advanced identity-threat detections | Spot identity cyberthreats in real time with preconfigured alerts and detections for common and emerging cyberattack patterns. |
| Powerful automation | Respond to threats at machine speed. Immediately restrict identities confirmed as compromised so they can’t persist in your organization or be further exploited. |
| Streamlined deployment | Quickly activate identity protections for qualifying on-premises infrastructure with the new pre-installed agent. |
| Enhanced identity inventory | Deliver true identity-level insights with linkages between accounts across environments, applications, and vendors. |
| Non-human identity protection | Monitor, secure, and manage non-human identities across your organization with Microsoft Defender for Identity. |
Pricing Notes:
- All Prices are Inclusive of GST
- Pricing and product availability subject to change without notice.
Our Price: Request a Quote
Our Price: Request a Quote
Our Price: Request a Quote